As technologists, we’ve all been convinced that automation is the solution to our problems. But augmentation is what we really need. We just don’t know it yet…
There is no discipline where this is more true than security. We’re constantly overmatched and under-resourced. Threats come at us from around the globe and at any time. The better we can scale the limited number of humans we have to protect our companies, the safer we will be.
The roots of our false sense of belief in automation are deep-seated. Take a look at marketing for nearly any security product. You’re bound to see automation as one of the core value props. When a belief is so pervasive, it’s hard to avoid it without consciously taking a step back to reexamine its accuracy.
Why do we allow ourselves to fall for this too-good-to-be-true story? Because we’re human, and humans are fallible. The promise of automation makes us believe the right tool can make our problems go away. And let’s face it: our companies would love for their security problems to magically disappear.
This is where our trouble begins. We either fall into the trap and put too much faith into automation, or we put up our defenses and become skeptics. We need to reframe our positive or negative views on automation and form a more nuanced opinion.
To accomplish this, we need to reevaluate our beliefs about automation and establish a new mental model about when to use automation, augmentation, and human intelligence.
The spectrum of security automation beliefs
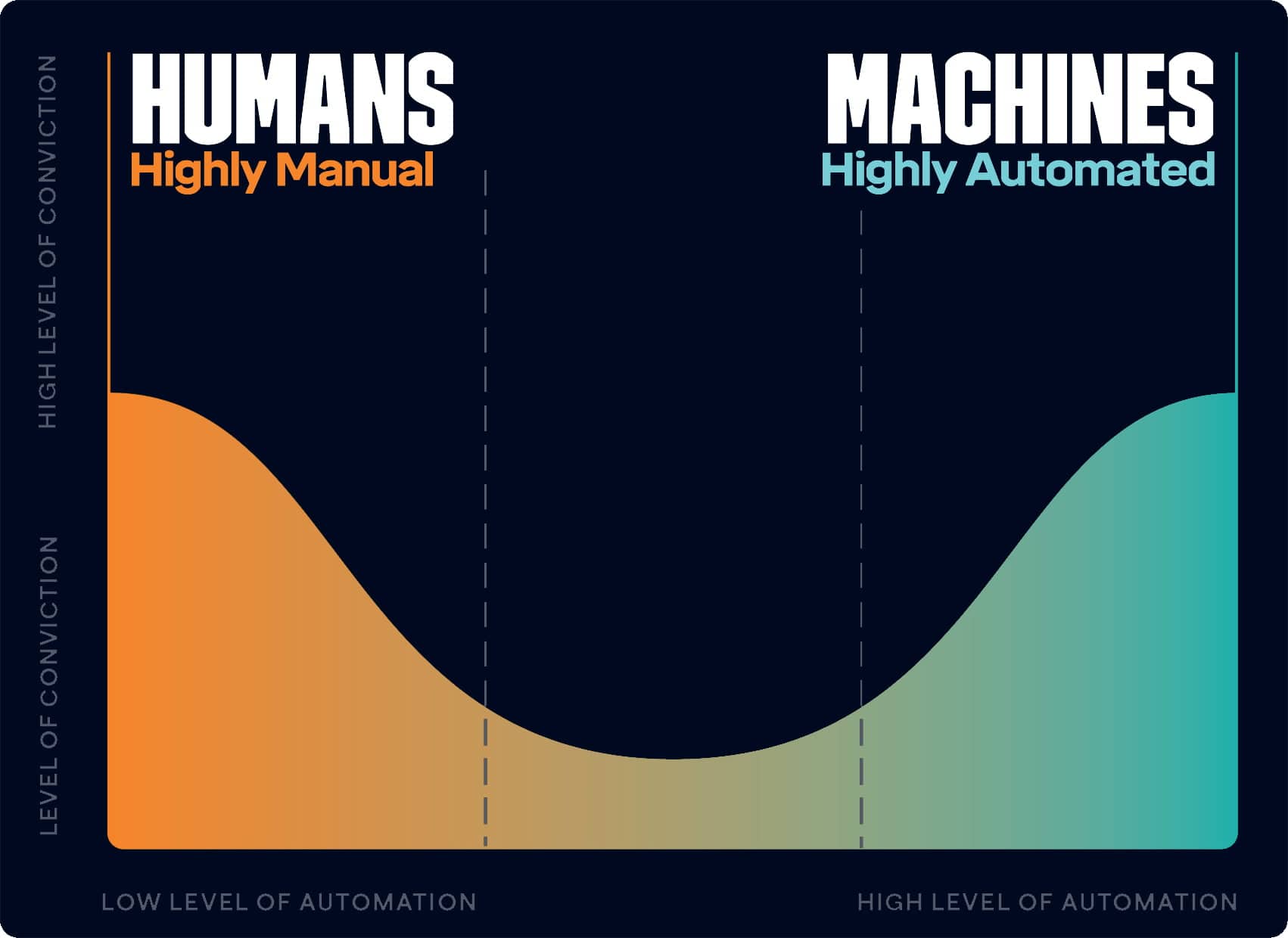
The first step towards determining when to use automation in our security programs is to understand where we fall on the spectrum of beliefs about security automation. The paradigm many of us follow tends to gravitate towards one end of the spectrum.
On one extreme, we’re so bullish on automation that we’ve falsely convinced ourselves we can automate everything. We try to automate tasks that have no business being automated, almost as an act of defiance.
Or, on another extreme, we’ve been burned so badly that we believe humans are the only reliable way to get things done. We insist on doing everything manually, even if it’s prohibitively expensive or tedious to do so.
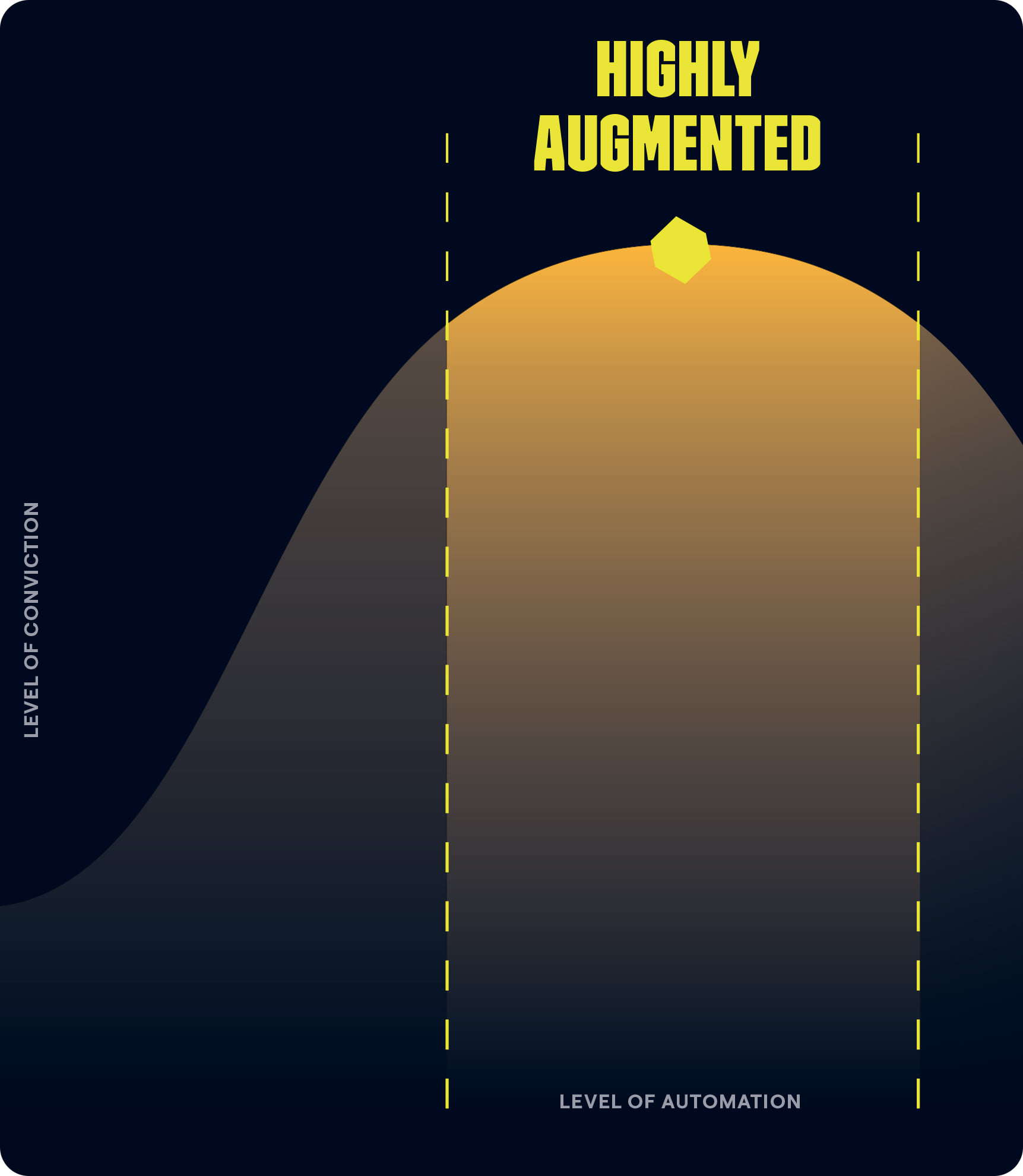
The paradigm of the future looks different. By reframing our mindset around the traditional view of automated vs. manual, we unlock a powerful new model.
If we can convince ourselves to prioritize augmentation over highly manual or highly automated processes, we end up with a more moderate and balanced view. The ideal mix for getting important work done is a combination of automation, human intelligence, and the true force multiplier: augmentation.
A prioritization model for security augmentation
Some forward-thinking leaders have already started to adopt this new augmentation-first paradigm. On a recent CISO Series podcast episode, LinkedIn CISO Geoff Belknap shared his perspective on automation:
“I’m not disappointed by what automation has delivered, but I think I have taken a very realistic view of what automation could do. Which is make smart humans able to make faster decisions, make better decisions.”
This is exactly the mindset we need to take towards automation. First, be realistic about what automation is capable of. With that expectation, focus on areas where augmentation can help humans make faster and better decisions. That’s the winning formula.
One way to help ourselves adopt this mindset is by using a model to guide our decision making.
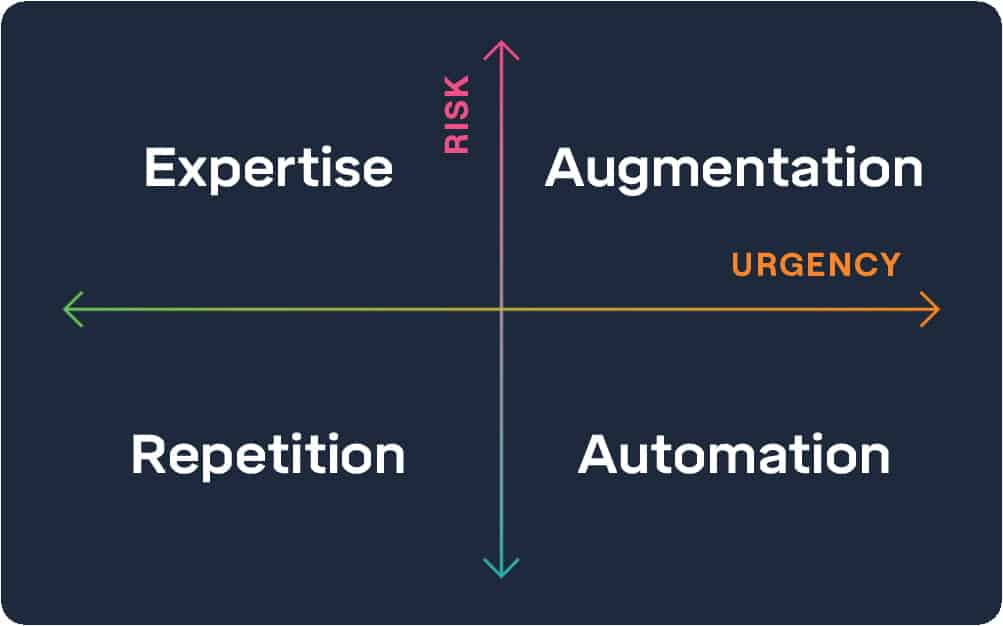
In our day-to-day lives as security professionals, most of our decision-making comes down to risk and urgency. Consciously or unconsciously, we spend our days triaging the tasks that come at us along these two vectors. As a result, they’re the axes in our model.
Our decision about the best way to execute different types of work comes down to specific criteria for each quadrant in the model. Based on where tasks map on the scale of risk and urgency, we can determine how to approach the work and the types of tools we should be using.
Augmentation
Tasks that are both high risk and high urgency should be augmented using a combination of human intelligence and machines. This is the area where both speed and quality matter. Any gains in speed from machines or judgment from humans can make a big difference. A few ideas specific to security are outlined in the next section.
Automation
Conversely, tasks that are low risk and high urgency are good candidates for automation. They’re important enough to be done, but not complex enough where human intervention is valuable. Let the machines do the fast, repetitive work.
Processes like access provisioning are great candidates for automation. Once roles or business rules have been established and applications have been integrated with access control systems, certain access can be automatically granted for every new employee. Human intervention is only needed for exceptions or errors.

Expertise
Tasks that are high risk and low urgency typically require expertise, or human intelligence, to be completed. They’re complex enough that creativity and time to weigh potential options is valuable. People with specific expertise are best suited for this type of work.
Security strategy, architecture, and engineering are inherently creative exercises. They’re high risk because the wrong strategy, architecture, or system design can have catastrophic consequences. However, machines can contribute relatively little to the creative process. In this case, it’s best to let the experts do their work.
Subscribe for monthly updates

Repetition
Finally, tasks that are low risk and low urgency but still need to be done can be executed through manual repetition. As much as we’d like to augment or automate everything, we have to prioritize. Sometimes a manual process is good enough.
For example, monitoring and following up on security policy exceptions is a repetitive task that’s more effective with a human touch. Instead of sending out automated reminders that are easy to ignore, it’s often better for a human to do the work.
Security augmentation in the real world
New tools create new opportunities for augmentation in security. Here are a few ideas about how to start using augmentation in your own work.
Fraud detection
An early example of human augmentation in security is PayPal’s approach for fighting fraud. As recounted by Peter Thiel in Zero to One, the young company had more than $10 million losses from fraud each month.
PayPal engineers first built an automated system that was ineffective because fraudsters adapted their techniques. However, they discovered an augmented approach was highly effective. Thiel described the incredible results:
“This kind of man-machine symbiosis enabled PayPal to stay in business, which in turn enabled hundreds of thousands of small businesses to accept the payments they needed to thrive on the internet. None of it would have been possible without the man-machine solution—even though most people would never see it or even hear about it.”
Instead of relying solely on automation, PayPal added the power of human judgment to mitigate fraud. The solution was so impactful that it saved the company.
Risk and compliance
Risk and compliance is a notoriously manual process that is starting to see the benefits of augmentation. A new generation of continuous compliance tools like Drata, Secureframe, and Vanta has entered the market.
Augment your compliance teams with these tools to manage evidence collection workflows, reporting, and testing. Save your people for designing controls, interpreting results, and remediating any issues that come up. When implemented effectively, you can reduce your compliance timelines from months to weeks.
Application security testing
Engineering teams are continuously under pressure to move fast and ship. Manual application security reviews add friction and decrease velocity.
Security teams can be augmented by embedding automated vulnerability scanning into development and build processes. Using automation strategically can allow your security teams to focus manual reviews on specific areas of risk and save hours of effort for each release.
Incident detection and response
When investigating security incidents, one of the biggest challenges engineers have is quickly and accurately identifying anomalous events. More data means more false positives. That’s a distraction when time is of the essence.
Incident detection and response engineers can augment themselves by iteratively building automated detection rules as they see anomalous events in the environment. High quality rules benefit the entire team by cutting down on false positives so real incidents can be identified faster.
Cloud configuration management
Monitoring and maintaining cloud security configurations is a daunting task, particularly in multi-cloud environments. One small change can open a gaping hole and expose your cloud infrastructure to significant risks.
This process can be augmented by continuously scanning your cloud configurations with cloud workload protection platforms. Automating checks for misconfigurations means you’ll find them faster and don’t need humans to intervene until anomalies are found.
Email security
Employees send and receive thousands of emails per day and are continuously targeted by attackers. As Forrester noted in a recent study, security teams spend up to 600 hours each month addressing email security incidents. It’s impossible to keep up with all the threats your employees are facing.
Augment your employees and security teams using platforms like Tessian to alert users when they’re seeing a suspicious email or potentially sharing sensitive data. Engaging people in-the-moment is far more effective than investigating incidents and remediating data loss after they’ve occurred.
Security’s augmented future
The next evolution of security is going to be led by augmentation, not automation. The greatest value comes from combining humans and machines and letting each do what they’re best at. In the famous words of mathematician Richard Hamming:
“Machines should work. People should think.”
It’s unfair to view tools as magic bullets. They’re not going to solve all our problems. However, it’s equally as unfair to view tools as enemies. We can’t expect people to do everything on their own — they need tools.
Top security leaders are making strategic choices about how and when to use automation, augmentation, and human intelligence. The stakes are higher than ever. The right choices can be the difference between a good night’s sleep and becoming another news headline.

Cole Grolmus










